为了加入亚马逊广告联盟大家庭,不得已去申请https证书,这玩意是经过rss加密的,据说更安全。
一、ssl证书申请
申请证书的网址是https://freessl.cn,现在不弄个https浏览器都会认为网站不安全了。
在上面的证书网站上注册了,并且写入了本网站的域名之后,跳出对话框,下载一个叫做KeyManager的软件,哇塞要设置主密码,而后软件给出一个无比复杂的密码之后一闪而过,都没看清,这个密码应该是用来找回主密码用的,KeyManager说不怕,可以找回,暂且不表。
接下来回到fressl.cn进行域名验证,根据提示信息到阿里云(我的域名服务商)去添加一条txt解析,并且删除了一些废弃的cname,来让中国大陆、香港和美国的服务器都能没有歧义地访问我的网站。
验证之后有个10分钟左右就领到证书,如果是在KeyManager中操作(申请、验证)的话,到这一步会有一个按钮叫“一键部署”,点下去就是一片白屏完全卡主。到fressl.cn下载了证书,安装到了网站后台,结果没有用。猜测是缺少了公钥和私钥,只有chain。
放弃。(后来的事情证明,是当时没有完全理解freessl.cn的套路,上面提到的一套文件都可以get到)
看到阿里云上提供免费证书,果断过去搞。
购买一个免费的证书,颁发过程类似,也需要域名验证,发下来的证书简要信息如下:实例:cas-cn-45918knmh107证书名称:cert-2431434证书来源:购买证书类型:DV绑定域名:www.oaphy.com,oaphy.com颁发厂商:Symantec有效期限:1年签发时间:2019年7月29日到期时间:2020年7月28日二、ssl证书安装在/etc/apache2下建立/cert文件夹,把下载的公钥私钥和证书全都ftp上去,修改sites-available文件夹下的000-default.conf增加SSLProtocal all -SSLv2SSLCertificateFile 公钥文件(crt后缀)SSLCertificateKeyFile 私钥文件(key后缀)SSLCertificateChainFile 证书文件(crt后缀)启动ssl服务sudo a2enmod ssl结果发现访问网站虽然已经变成https风格,但还是被浏览器提示不安全,在https://www.geocerts.com/ssl-checker检查后发现问题
Certificate Common Name (CN) and Hostname Match?
证书公共名与主机名不一致。
无奈去修改主机名,改成www.oaphy.com,吊销原证书,重新申请证书。
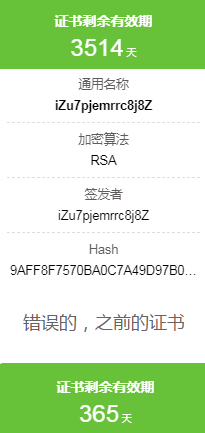
折腾了半天,原来不是证书问题而是端口问题,在用KeyManager软件中的“证书扫描”功能时意外发现,扫80端口的证书就是对的,扫443端口的证书就是以前的错的那个。
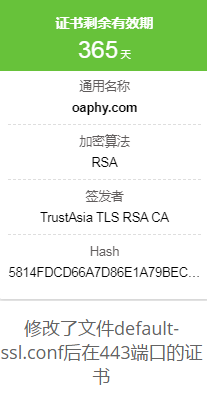
这时候意识到去修改/etc/apache2/sites-available/default-ssl.conf,将公钥私钥和证书文件的位置都改好,之后就大功告成了。
现在可以正常访问清爽的https风格的网站,但是http风格的就不行了。如果不处理http问题,可能会出现You’re speaking plain HTTP to an SSL-enabled server port问题,意思是在http协议端口使用了https协议语法。
原因是在上面漫长的调试过程中修改了80端口配置,让他也在ssl模式下工作,再回到000-default.conf中去,把<VirtualHost *:80>标签里的ssl相关设定统统注释掉。
为了能重定向http到https,还需要在这里继续加入下面的三行
- RewriteEngine on
- RewriteCond %{HTTPS} !=on
- RewriteRule ^(.*) https://%{SERVER_NAME}$1 [L,R]
并启动重定向
sudo a2enmod rewrite
保存退出,重启apache2,就可以了。
附录:
000-default.conf
<VirtualHost *:80>
# The ServerName directive sets the request scheme, hostname and port that
# the server uses to identify itself. This is used when creating
# redirection URLs. In the context of virtual hosts, the ServerName
# specifies what hostname must appear in the request's Host: header to
# match this virtual host. For the default virtual host (this file) this
# value is not decisive as it is used as a last resort host regardless.
# However, you must set it for any further virtual host explicitly.
#ServerName www.example.com
ServerAdmin webmaster@localhost
DocumentRoot /var/www/html
# Available loglevels: trace8, ..., trace1, debug, info, notice, warn,
# error, crit, alert, emerg.
# It is also possible to configure the loglevel for particular
# modules, e.g.
#LogLevel info ssl:warn
ErrorLog ${APACHE_LOG_DIR}/error.log
CustomLog ${APACHE_LOG_DIR}/access.log combined
#SSLEngine on
#SSLCertificateFile /etc/apache2/cert/oaphy.com.crt
#SSLCertificateKeyFile /etc/apache2/cert/oaphy.com_key.key
#SSLCertificateChainFile /etc/apache2/cert/ca_bundle.crt
#SSLProtocol all -SSLv2
#SSLCipherSuite HIGH:!RC4:!MD5:!aNULL:!eNULL:!NULL:!DH:!EDH:!EXP:+MEDIUM
#SSLHonorCipherOrder on
ServerName oaphy.com
# For most configuration files from conf-available/, which are
# enabled or disabled at a global level, it is possible to
# include a line for only one particular virtual host. For example the
# following line enables the CGI configuration for this host only
# after it has been globally disabled with "a2disconf".
#Include conf-available/serve-cgi-bin.conf
RewriteEngine on
RewriteCond %{HTTPS} !=on
RewriteRule ^(.*) https://%{SERVER_NAME}$1 [L,R=301]
DocumentRoot /var/www/html/futures
Servername futures.oaphy.com
Serveralias futures.oaphy.com
</VirtualHost>
<VirtualHost *:443>
# The ServerName directive sets the request scheme, hostname and port that
# the server uses to identify itself. This is used when creating
# redirection URLs. In the context of virtual hosts, the ServerName
# specifies what hostname must appear in the request's Host: header to
# match this virtual host. For the default virtual host (this file) this
# value is not decisive as it is used as a last resort host regardless.
# However, you must set it for any further virtual host explicitly.
#ServerName www.example.com
ServerAdmin webmaster@localhost
DocumentRoot /var/www/html
# Available loglevels: trace8, ..., trace1, debug, info, notice, warn,
# error, crit, alert, emerg.
# It is also possible to configure the loglevel for particular
# modules, e.g.
#LogLevel info ssl:warn
ErrorLog ${APACHE_LOG_DIR}/error.log
CustomLog ${APACHE_LOG_DIR}/access.log combined
SSLEngine on
SSLCertificateFile /etc/apache2/cert/oaphy.com.crt
SSLCertificateKeyFile /etc/apache2/cert/oaphy.com_key.key
SSLCertificateChainFile /etc/apache2/cert/ca_bundle.crt
SSLProtocol all -SSLv2
SSLCipherSuite HIGH:!RC4:!MD5:!aNULL:!eNULL:!NULL:!DH:!EDH:!EXP:+MEDIUM
SSLHonorCipherOrder on
ServerName oaphy.com
# For most configuration files from conf-available/, which are
# enabled or disabled at a global level, it is possible to
# include a line for only one particular virtual host. For example the
# following line enables the CGI configuration for this host only
# after it has been globally disabled with "a2disconf".
#Include conf-available/serve-cgi-bin.conf
#Subdomain
</VirtualHost>
# vim: syntax=apache ts=4 sw=4 sts=4 sr noet
<VirtualHost *:80>
ServerAdmin [email protected]
DocumentRoot /var/www/html/futures
ServerName futures.oaphy.com
ServerAlias futures.oaphy.com
</VirtualHost>
<VirtualHost *:443>
ServerAdmin [email protected]
DocumentRoot /var/www/html/futures
ServerName futures.oaphy.com
ServerAlias futures.oaphy.com
SSLEngine on
SSLCertificateFile /etc/apache2/cert/oaphy.com.crt
SSLCertificateKeyFile /etc/apache2/cert/oaphy.com_key.key
SSLCertificateChainFile /etc/apache2/cert/ca_bundle.crt
SSLProtocol all -SSLv2
SSLCipherSuite HIGH:!RC4:!MD5:!aNULL:!eNULL:!NULL:!DH:!EDH:!EXP:+MEDIUM
SSLHonorCipherOrder on
</VirtualHost>default-ssl.conf
<IfModule mod_ssl.c>
<VirtualHost _default_:443>
ServerAdmin webmaster@localhost
DocumentRoot /var/www/html
# Available loglevels: trace8, ..., trace1, debug, info, notice, warn,
# error, crit, alert, emerg.
# It is also possible to configure the loglevel for particular
# modules, e.g.
#LogLevel info ssl:warn
ErrorLog ${APACHE_LOG_DIR}/error.log
CustomLog ${APACHE_LOG_DIR}/access.log combined
# For most configuration files from conf-available/, which are
# enabled or disabled at a global level, it is possible to
# include a line for only one particular virtual host. For example the
# following line enables the CGI configuration for this host only
# after it has been globally disabled with "a2disconf".
#Include conf-available/serve-cgi-bin.conf
# SSL Engine Switch:
# Enable/Disable SSL for this virtual host.
SSLEngine on
# A self-signed (snakeoil) certificate can be created by installing
# the ssl-cert package. See
# /usr/share/doc/apache2/README.Debian.gz for more info.
# If both key and certificate are stored in the same file, only the
# SSLCertificateFile directive is needed.
# Server Certificate Chain:
# Point SSLCertificateChainFile at a file containing the
# concatenation of PEM encoded CA certificates which form the
# certificate chain for the server certificate. Alternatively
# the referenced file can be the same as SSLCertificateFile
# when the CA certificates are directly appended to the server
# certificate for convinience.
SSLCertificateFile /etc/apache2/cert/oaphy.com.crt
SSLCertificateKeyFile /etc/apache2/cert/oaphy.com_key.key
SSLCertificateChainFile /etc/apache2/cert/ca_bundle.crt
# Certificate Authority (CA):
# Set the CA certificate verification path where to find CA
# certificates for client authentication or alternatively one
# huge file containing all of them (file must be PEM encoded)
# Note: Inside SSLCACertificatePath you need hash symlinks
# to point to the certificate files. Use the provided
# Makefile to update the hash symlinks after changes.
#SSLCACertificatePath /etc/ssl/certs/
#SSLCACertificateFile /etc/apache2/ssl.crt/ca-bundle.crt
# Certificate Revocation Lists (CRL):
# Set the CA revocation path where to find CA CRLs for client
# authentication or alternatively one huge file containing all
# of them (file must be PEM encoded)
# Note: Inside SSLCARevocationPath you need hash symlinks
# to point to the certificate files. Use the provided
# Makefile to update the hash symlinks after changes.
#SSLCARevocationPath /etc/apache2/ssl.crl/
#SSLCARevocationFile /etc/apache2/ssl.crl/ca-bundle.crl
# Client Authentication (Type):
# Client certificate verification type and depth. Types are
# none, optional, require and optional_no_ca. Depth is a
# number which specifies how deeply to verify the certificate
# issuer chain before deciding the certificate is not valid.
#SSLVerifyClient require
#SSLVerifyDepth 10
# SSL Engine Options:
# Set various options for the SSL engine.
# o FakeBasicAuth:
# Translate the client X.509 into a Basic Authorisation. This means that
# the standard Auth/DBMAuth methods can be used for access control. The
# user name is the `one line' version of the client's X.509 certificate.
# Note that no password is obtained from the user. Every entry in the user
# file needs this password: `xxj31ZMTZzkVA'.
# o ExportCertData:
# This exports two additional environment variables: SSL_CLIENT_CERT and
# SSL_SERVER_CERT. These contain the PEM-encoded certificates of the
# server (always existing) and the client (only existing when client
# authentication is used). This can be used to import the certificates
# into CGI scripts.
# o StdEnvVars:
# This exports the standard SSL/TLS related `SSL_*' environment variables.
# Per default this exportation is switched off for performance reasons,
# because the extraction step is an expensive operation and is usually
# useless for serving static content. So one usually enables the
# exportation for CGI and SSI requests only.
# o OptRenegotiate:
# This enables optimized SSL connection renegotiation handling when SSL
# directives are used in per-directory context.
#SSLOptions +FakeBasicAuth +ExportCertData +StrictRequire
<FilesMatch "\.(cgi|shtml|phtml|php)$">
SSLOptions +StdEnvVars
</FilesMatch>
<Directory /usr/lib/cgi-bin>
SSLOptions +StdEnvVars
</Directory>
# SSL Protocol Adjustments:
# The safe and default but still SSL/TLS standard compliant shutdown
# approach is that mod_ssl sends the close notify alert but doesn't wait for
# the close notify alert from client. When you need a different shutdown
# approach you can use one of the following variables:
# o ssl-unclean-shutdown:
# This forces an unclean shutdown when the connection is closed, i.e. no
# SSL close notify alert is send or allowed to received. This violates
# the SSL/TLS standard but is needed for some brain-dead browsers. Use
# this when you receive I/O errors because of the standard approach where
# mod_ssl sends the close notify alert.
# o ssl-accurate-shutdown:
# This forces an accurate shutdown when the connection is closed, i.e. a
# SSL close notify alert is send and mod_ssl waits for the close notify
# alert of the client. This is 100% SSL/TLS standard compliant, but in
# practice often causes hanging connections with brain-dead browsers. Use
# this only for browsers where you know that their SSL implementation
# works correctly.
# Notice: Most problems of broken clients are also related to the HTTP
# keep-alive facility, so you usually additionally want to disable
# keep-alive for those clients, too. Use variable "nokeepalive" for this.
# Similarly, one has to force some clients to use HTTP/1.0 to workaround
# their broken HTTP/1.1 implementation. Use variables "downgrade-1.0" and
# "force-response-1.0" for this.
# BrowserMatch "MSIE [2-6]" \
# nokeepalive ssl-unclean-shutdown \
# downgrade-1.0 force-response-1.0
</VirtualHost>
</IfModule>
# vim: syntax=apache ts=4 sw=4 sts=4 sr noet
<IfModule mod_ssl.c>
<VirtualHost _default_:443>
DocumentRoot /var/www/html/futures
ServerName futures.oaphy.com
ServerName futures.oaphy.com
SSLEngine on
SSLCertificateFile /etc/apache2/cert/oaphy.com.crt
SSLCertificateKeyFile /etc/apache2/cert/oaphy.com_key.key
SSLCertificateChainFile /etc/apache2/cert/ca_bundle.crt
</VirtualHost>
</IfModule>